OpenVPN (Ubuntu 16.04): Unterschied zwischen den Versionen
(→Links) |
|||
| (14 dazwischenliegende Versionen desselben Benutzers werden nicht angezeigt) | |||
| Zeile 1: | Zeile 1: | ||
== Installation == | == Installation == | ||
<div class="mw-collapsible mw-collapsed"> | |||
Um die Installation anzuzeigen bitte aufklappen | |||
<div class="mw-collapsible-content"> | |||
<pre> | <pre> | ||
| Zeile 9: | Zeile 12: | ||
sudo cp -r /usr/share/easy-rsa /etc/openvpn/easy-rsa2 | sudo cp -r /usr/share/easy-rsa /etc/openvpn/easy-rsa2 | ||
</pre> | </pre> | ||
</div> | |||
</div> | |||
== Konfiguration == | == Konfiguration == | ||
<div class="mw-collapsible mw-collapsed"> | |||
Um die allgemeine Konfiguration anzuzeigen bitte aufklappen | |||
<div class="mw-collapsible-content"> | |||
=== Beispiele === | === Beispiele === | ||
| Zeile 84: | Zeile 92: | ||
tar -cf ersterClient.tar ersterClient.key ersterClient.crt ca.crt | tar -cf ersterClient.tar ersterClient.key ersterClient.crt ca.crt | ||
</pre> | </pre> | ||
</div> | |||
</div> | |||
== Client Konfiguration == | == Client Konfiguration == | ||
<div class="mw-collapsible mw-collapsed"> | |||
Um die Client-Konfiguration anzuzeigen bitte aufklappen | |||
<div class="mw-collapsible-content"> | |||
=== Beispiel einer ''client.conf''-Konfigurationsdatei === | === Beispiel einer ''client.conf''-Konfigurationsdatei === | ||
<pre | <pre> | ||
############################################## | ############################################## | ||
# Sample client-side OpenVPN 2.0 config file # | # Sample client-side OpenVPN 2.0 config file # | ||
| Zeile 236: | Zeile 245: | ||
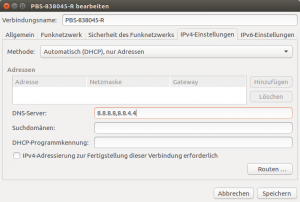
[[Datei:Networkmanager_IPv4.png|300px|Networkmanager IPv4-Settings]] | [[Datei:Networkmanager_IPv4.png|300px|Networkmanager IPv4-Settings]] | ||
</div> | |||
</div> | |||
== Server Konfiguration == | == Server Konfiguration == | ||
<div class="mw-collapsible mw-collapsed"> | |||
Um die Server-Konfiguration anzuzeigen bitte aufklappen | |||
<div class="mw-collapsible-content"> | |||
=== IPV4-Weiterleitung aktivieren === | === IPV4-Weiterleitung aktivieren === | ||
| Zeile 532: | Zeile 546: | ||
ifconfig-push 10.8.0.8 255.255.255.0 | ifconfig-push 10.8.0.8 255.255.255.0 | ||
</pre> | </pre> | ||
</div> | |||
</div> | |||
== Verbindungsaufbau über Terminal == | == Verbindungsaufbau über Terminal == | ||
<div class="mw-collapsible mw-collapsed"> | |||
Um den Verbindungsaufbau über ein Terminal anzuzeigen bitte aufklappen | |||
<div class="mw-collapsible-content"> | |||
Konfigurationen unter <code>/etc/openvpn/clients/</code> hinterlegen. | Konfigurationen unter <code>/etc/openvpn/clients/</code> hinterlegen. | ||
| Zeile 563: | Zeile 582: | ||
if [ $? -ne 0 ] && echo "Failed to disconnect from VPN Server using ${1}.ovpn..." && exit 1; | if [ $? -ne 0 ] && echo "Failed to disconnect from VPN Server using ${1}.ovpn..." && exit 1; | ||
</pre> | </pre> | ||
</div> | |||
</div> | |||
== Links == | == Links == | ||
| Zeile 569: | Zeile 590: | ||
Zurück zu [[Ubuntu]] | Zurück zu [[OpenVPN (Ubuntu)#Routed|OpenVPN]] | ||
Aktuelle Version vom 4. April 2023, 18:47 Uhr
Installation
Um die Installation anzuzeigen bitte aufklappen
sudo apt-get install openvpn easy-rsa
Ordner zur Schlüsselerzeugung kopieren:
sudo cp -r /usr/share/easy-rsa /etc/openvpn/easy-rsa2
Konfiguration
Um die allgemeine Konfiguration anzuzeigen bitte aufklappen
Beispiele
/usr/share/doc/openvpn/examples/
Schlüssel und Zertifikate generieren
Variablen anpassen
In das RSA-Verzeichnis wechseln:
cd /etc/openvpn/easy-rsa2/
Die Datei /etc/openvpn/easy-rsa2/vars anpassen:
sudo nano vars
Am Ende folgenden Alias-Eintrag hinzufügen:
export KEY_ALTNAMES="Irgendwas"
Weitere Vorbereitungen
Schlüssel-Verzeuchnis anlegen:
sudo mkdir /etc/openvpn/easy-rsa2/keys
Neueste openssl-X.X.X.cnf kopieren:
sudo cp openssl-1.0.0.cnf openssl.cnf
Datei vars in die Umgebungsvariablen aufnehmen:
source ./vars
Schlüssel erzeugen
sudo -E ./clean-all sudo -E ./build-ca
Server Zertifikat und Schlüssel erstellen (Common Name sollte DNS-Name sein):
sudo -E ./build-key-server server
Benutzerschlüssel anlegen:
- Common Name ist der Name, mit dem ein Client später identifiziert wird (kein DNS-Name).
- Bei Meldung TXT_DB error number 2 einen anderen Common Name verwenden (wurde schon verwendet).
sudo -E ./build-key ersterClient sudo -E ./build-key zweiterClient ...
Diffie-Hellman-Parameter generieren:
sudo -E ./build-dh
Client-Schlüssel in eine Datei packen:
tar -cf ersterClient.tar ersterClient.key ersterClient.crt ca.crt
Client Konfiguration
Um die Client-Konfiguration anzuzeigen bitte aufklappen
Beispiel einer client.conf-Konfigurationsdatei
############################################## # Sample client-side OpenVPN 2.0 config file # # for connecting to multi-client server. # # # # This configuration can be used by multiple # # clients, however each client should have # # its own cert and key files. # # # # On Windows, you might want to rename this # # file so it has a .ovpn extension # ############################################## # Specify that we are a client and that we # will be pulling certain config file directives # from the server. client # Use the same setting as you are using on # the server. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # Are we connecting to a TCP or # UDP server? Use the same setting as # on the server. ;proto tcp proto udp # The hostname/IP and port of the server. # You can have multiple remote entries # to load balance between the servers. remote <ip or dns name> 10000 # Keep trying indefinitely to resolve the # host name of the OpenVPN server. Very useful # on machines which are not permanently connected # to the internet such as laptops. resolv-retry infinite # Most clients don't need to bind to # a specific local port number. nobind # SSL/TLS parms. # See the server config file for more # description. It's best to use # a separate .crt/.key file pair # for each client. A single ca # file can be used for all clients. ca ./keys_linux_server/ca.crt cert ./keys_linux_server/server.crt key ./keys_linux_server/server.key # Verify server certificate by checking # that the certicate has the nsCertType # field set to "server". This is an # important precaution to protect against # a potential attack discussed here: # http://openvpn.net/howto.html#mitm # # To use this feature, you will need to generate # your server certificates with the nsCertType # field set to "server". The build-key-server # script in the easy-rsa folder will do this. ns-cert-type server # Select a cryptographic cipher. # If the cipher option is used on the server # then you must also specify it here. cipher AES-256-CBC # Enable compression on the VPN link. # Don't enable this unless it is also # enabled in the server config file. comp-lzo # Set log file verbosity. verb 3 pull auth SHA1 auth-user-pass
Route hinzufügen
Wenn der OpenVPN-Server so konfiguriert wurde, dass das dahinterliegende Netzwerk erreicht werden kann, dann müssen die erreichbaren Rechner, in dem dahinterliegenden Netzwerk, die Route zurück zum Server kennen. Andernfalls schlägt die Verbindung fehl, weil die Pakete den Weg zurück nicht finden.
Falls möglich, sollte man die Route beim Router hinterlegen. Falls dies jedoch nicht möglich ist, muss bei jedem Rechner direkt eine Route hinterlegt werden.
Dazu in der Datei /etc/network/interfaces/ folgende Zeile hinzufügen:
# Add persitent route command post-up route add -net <network> netmask 255.255.255.0 gw <openvpn server> metric 1
Beispiel:
post-up route add -net 10.9.0.0 netmask 255.255.255.0 gw 10.0.0.100 metric 1
Gesetzte Routen anzeigen lassen:
netstat -r
Masquerade hinzufügen
Der Client-Internetverkehr kann mittels folgender Zeile (in der server.conf) vollständig über den VPN-Server geleitet werden:
push "redirect-gateway def1 bypass-dhcp"
Damit der externe Netzverkehr funktioniert, muss in der Datei /etc/network/interfaces/ (auf dem VPN-Server) folgende Zeile hinzufügt werden:
up iptables -t nat -A POSTROUTING -s 10.8.1.0/24 -o eth0 -j MASQUERADE
Client GUI
OpenVPN-GUI installieren (falls nicht vorinstalliert):
sudo apt-get install network-manager-openvpn network-manager-openvpn-gnome
Danach die Datei xxxxxx.ovpn mittels Gespeicherte VPN-Konfiguration importieren... hinzufügen.
Siehe auch https://torguard.net/knowledgebase.php?action=displayarticle&id=53
Probleme
DNS-Umleitung funktioniert nicht unter Ubuntu 16.04
Dazu im Network Manager die Methode Automatisch (DHCP) auf Automatisch (DHCP), nur Adressen umstellen. Danach müssen die DNS-Server, die verwendet werden sollen, wenn keine OpenVPN-Verbindung besteht, angegeben werden.
Server Konfiguration
Um die Server-Konfiguration anzuzeigen bitte aufklappen
IPV4-Weiterleitung aktivieren
Siehe dazu Netzwerk einrichten (Linux)
Benutzer openvpn anlegen
Zur Erhöhung der Sicherheit wird der Server mit dem Benutzer openvpn ausgeführt.
Zum Anlegen eines systemspezifischen Benutzers siehe User Administration
Beispeil einer server.conf-Konfigurationsdatei
################################################# # Sample OpenVPN 2.0 config file for # # multi-client server. # # # # This file is for the server side # # of a many-clients <-> one-server # # OpenVPN configuration. # # # # OpenVPN also supports # # single-machine <-> single-machine # # configurations (See the Examples page # # on the web site for more info). # # # # This config should work on Windows # # or Linux/BSD systems. Remember on # # Windows to quote pathnames and use # # double backslashes, e.g.: # # "C:\\Program Files\\OpenVPN\\config\\foo.key" # # # # Comments are preceded with '#' or ';' # ################################################# # Which local IP address should OpenVPN # listen on? (optional) local 10.0.0.101 # Which TCP/UDP port should OpenVPN listen on? # If you want to run multiple OpenVPN instances # on the same machine, use a different port # number for each one. You will need to # open up this port on your firewall. port 10000 # TCP or UDP server? ;proto tcp proto udp # "dev tun" will create a routed IP tunnel, # "dev tap" will create an ethernet tunnel. # Use "dev tap0" if you are ethernet bridging # and have precreated a tap0 virtual interface # and bridged it with your ethernet interface. # If you want to control access policies # over the VPN, you must create firewall # rules for the the TUN/TAP interface. # On non-Windows systems, you can give # an explicit unit number, such as tun0. # On Windows, use "dev-node" for this. # On most systems, the VPN will not function # unless you partially or fully disable # the firewall for the TUN/TAP interface. ;dev tap dev tun # SSL/TLS root certificate (ca), certificate # (cert), and private key (key). Each client # and the server must have their own cert and # key file. The server and all clients will # use the same ca file. # # See the "easy-rsa" directory for a series # of scripts for generating RSA certificates # and private keys. Remember to use # a unique Common Name for the server # and each of the client certificates. # # Any X509 key management system can be used. # OpenVPN can also use a PKCS #12 formatted key file # (see "pkcs12" directive in man page). ca ./easy-rsa2/keys/ca.crt cert ./easy-rsa2/keys/server.crt key ./easy-rsa2/keys/server.key # This file should be kept secret # Diffie hellman parameters. # Generate your own with: # openssl dhparam -out dh1024.pem 1024 # Substitute 2048 for 1024 if you are using # 2048 bit keys. dh ./easy-rsa2/keys/dh2048.pem # Configure server mode and supply a VPN subnet # for OpenVPN to draw client addresses from. # The server will take 10.8.0.1 for itself, # the rest will be made available to clients. # Each client will be able to reach the server # on 10.8.0.1. Comment this line out if you are # ethernet bridging. See the man page for more info. server 10.8.0.0 255.255.255.0 # In subnet topology, the tun device is configured # with an IP and netmask like a "traditional" # broadcast-based network. topology subnet # Maintain a record of client <-> virtual IP address # associations in this file. If OpenVPN goes down or # is restarted, reconnecting clients can be assigned # the same virtual IP address from the pool that was # previously assigned. ifconfig-pool-persist ipp.txt # Push routes to the client to allow it # to reach other private subnets behind # the server. Remember that these # private subnets will also need # to know to route the OpenVPN client # address pool (10.8.0.0/255.255.255.0) # back to the OpenVPN server. push "route 10.0.0.0 255.255.255.0" # If enabled, this directive will configure # all clients to redirect their default # network gateway through the VPN, causing # all IP traffic such as web browsing and # and DNS lookups to go through the VPN # (The OpenVPN server machine may need to NAT # or bridge the TUN/TAP interface to the internet # in order for this to work properly). push "redirect-gateway def1 bypass-dhcp" # Certain Windows-specific network settings # can be pushed to clients, such as DNS # or WINS server addresses. CAVEAT: # http://openvpn.net/faq.html#dhcpcaveats # The addresses below refer to the public # DNS servers provided by opendns.com. push "dhcp-option DNS 10.0.0.101" ;push "dhcp-option DNS 208.67.220.220" # The keepalive directive causes ping-like # messages to be sent back and forth over # the link so that each side knows when # the other side has gone down. # Ping every 10 seconds, assume that remote # peer is down if no ping received during # a 120 second time period. keepalive 10 120 # Select a cryptographic cipher. # This config item must be copied to # the client config file as well. ;cipher BF-CBC # Blowfish (default) cipher AES-256-CBC # AES ;cipher DES-EDE3-CBC # Triple-DES # Enable compression on the VPN link. # If you enable it here, you must also # enable it in the client config file. comp-lzo # It's a good idea to reduce the OpenVPN # daemon's privileges after initialization. # # You can uncomment this out on # non-Windows systems. user openvpn group openvpn # The persist options will try to avoid # accessing certain resources on restart # that may no longer be accessible because # of the privilege downgrade. persist-key persist-tun # Output a short status file showing # current connections, truncated # and rewritten every minute. status openvpn-status.log # By default, log messages will go to the syslog (or # on Windows, if running as a service, they will go to # the "\Program Files\OpenVPN\log" directory). # Use log or log-append to override this default. # "log" will truncate the log file on OpenVPN startup, # while "log-append" will append to it. Use one # or the other (but not both). ;log openvpn.log log-append openvpn.log # Set the appropriate level of log # file verbosity. # # 0 is silent, except for fatal errors # 4 is reasonable for general usage # 5 and 6 can help to debug connection problems # 9 is extremely verbose verb 3 tls-server auth SHA1 script-security 3 execve auth-user-pass-verify checklogin.sh via-env # This directive sets a client configuration directory, # which the OpenVPN server will scan for every # incomming connection, searching for a client specific # configuration file. client-config-dir ccd
Script checklogin.sh
cd /etc/openvpn/ sudo nano checklogin.sh
#!/bin/bash # zur Sicherheit if [ "$username" == "" -o "$password" == "" ] ; then exit 1 fi # Username und Passwort werden zusammengesetzt USER_PASS="$username:$password" # der Eintrag wird in der Datei users gesucht cat ./users | grep $USER_PASS > /dev/null # wenn grep den Eintrag gefunden hat, ist der Exitcode 0 exit $?
Besitzer ändern und ausführbar machen:
sudo chown openvpn:openvpn checklogin.sh sudo chmod a+x checklogin.sh
Inhalt der Datei users
sudo nano users
Benutzer:Passwort <user name>:<password>
sudo chown openvpn:openvpn users
client config dir (ccd)
Mit einer Datei im client config dir-Verzeichnis kann man einem Client eine statische IP-Adresse zuordnen
Zuerst ein Verzeichnis anlegen (muss mit der Direktive client-config-dir übereinstimmen), wo alle Dateien abgelegt werden:
cd /etc/openvpn/ sudo mkdir ccd
Danach eine Datei mit der Angabe Common Name beim Benutzerschlüssel anlegen:
sudo nano ccd/<common name>
Und folgenden Inhalt eintragen:
ifconfig-push <ip address> <net mask>
z.B.
ifconfig-push 10.8.0.8 255.255.255.0
Verbindungsaufbau über Terminal
Um den Verbindungsaufbau über ein Terminal anzuzeigen bitte aufklappen
Konfigurationen unter /etc/openvpn/clients/ hinterlegen.
Verbindung aufbauen:
#!/bin/sh
#check if profile has been passed
[ -z $1 ] && echo "Usage: ${0} <client>..." && exit 1;
openvpn --script-security 2 --config /etc/openvpn/clients/${1}.ovpn --auth-user-pass /etc/openvpn/clients/login.conf &
# check if call was successful
[ $? -ne 0 ] && echo "Failed to connect to VPN server using ${1}.ovpn... && exit 1;
Verbindung trennen:
#!/bin/sh
#check if profile has been passed
if [ -z $1 ] && echo "Usage: ${0} <client>..." && exit 1;
kill `sudo pgrep -fl ${1}.ovpn | grep openvpn | cut -d ' ' -f 1`
# check if kill was successfull
if [ $? -ne 0 ] && echo "Failed to disconnect from VPN Server using ${1}.ovpn..." && exit 1;
Links
http://forums.openvpn.net/topic7410.html
Zurück zu OpenVPN